How to Reduce Alert Noise by 90%
Without Missing Real Incidents
The Thesis
Most teams treat alert tuning as an art, tweaking thresholds by gut feel, silencing noisy alerts reactively, and hoping for the best.
But alert noise is a mathematically modelable problem. By treating thresholds as statistical parameters, you can quantify the exact tradeoff between noise and miss rate and optimize it scientifically.
1. The Alert Noise Problem
The average SRE team deals with hundreds to thousands of alerts per week, but only a fraction are actionable. According to industry data (like PagerDuty's State of Digital Operations), roughly 40-70% of alerts are noise.
The Real Cost
It is not just annoyance. It is alert fatigue leading to missed real incidents, engineer burnout, and severe attrition.
The Irony
Teams that over-alert to "be safe" end up less safe because human operators eventually stop paying attention to the boy who cried wolf.
Complementary reading: Check out our post on Shifting Alerts Left.
2. Why Gut-Feel Threshold Tuning Fails
Teams typically tune alerts through a process of "gut feel". When someone gets paged on a weekend for no reason, they bump the threshold up. When a real incident gets missed, they bump it down. This creates a constant oscillation between "too noisy" and "we missed something".
Set it too low and you drown in noise; set it too high and you miss real incidents entirely.
A CPU spike to 85% for 10 seconds is usually meaningless; for 10 minutes it is a problem. Yet, most teams set a single static for: 5m duration indiscriminately.
The same for duration is applied to wildly different metrics (CPU vs. error rate vs. latency) despite those metrics having completely different signal characteristics.
Teams adjust thresholds after incidents or noisy weekends, but they never systematically measure the statistical impact of that adjustment over historic data.
3. The Mathematical Framework
Modeling Alert Noise vs. Accuracy
This is the core idea to solve the noise problem. Stop relying on static limits. Start treating thresholds as adjustable parameters that you can measure and optimize.
3a. Defining the Variables
- VThreshold Value (e.g., CPU > 80%)
- DDuration Window (e.g., sustained for 5 minutes)
- NNoise Rate (FP)
- MMiss Rate (FN)
3b. The Tradeoff Surface
For any metric, you can plot an interactive tradeoff surface. Increasing V (stricter limit) reduces noise but strictly increases miss rate. However, increasing D (duration) is often the higher-leverage knob. A 2x increase in duration often cuts noise by 60-80% while increasing miss rate by only 5-10%.
Interactive Model: CPU > 80% Threshold
Datadog-style interactive timeline. Adjust duration to see false alerts drop.
Noise (Alerts/Month)
31
Missed Incidents
8
Insight: Moving from 1min to 5min duration naturally suppresses 91% of transient spikes (342 → 31). Watch the red incident markers physically vanish from the chart above as you increase the threshold duration. That 5min sweet spot is the Pareto frontier for CPU metrics.
3c. Signal Characteristics Matter
Different metrics have fundamentally different noise profiles. The right (V, D) pair is metric-specific, not a global standard.
CPU / Memory
Error Rates
Latency (p99)
Disk Usage
3d. Building the Model with Data
This is essentially a binary classification optimization problem, identical to precision/recall curves in Machine Learning.
- Export alert history (last 90 days).
- Label the data: mark each alert as actionable or noise.
- Replay with simulation: backtest what happens if you change
(V, D)on historic data. - Plot the Pareto frontier: find the combinations where you cannot reduce noise further without missing real incidents.
- Pick the operating point: decide your acceptable Miss Rate based on service criticality.
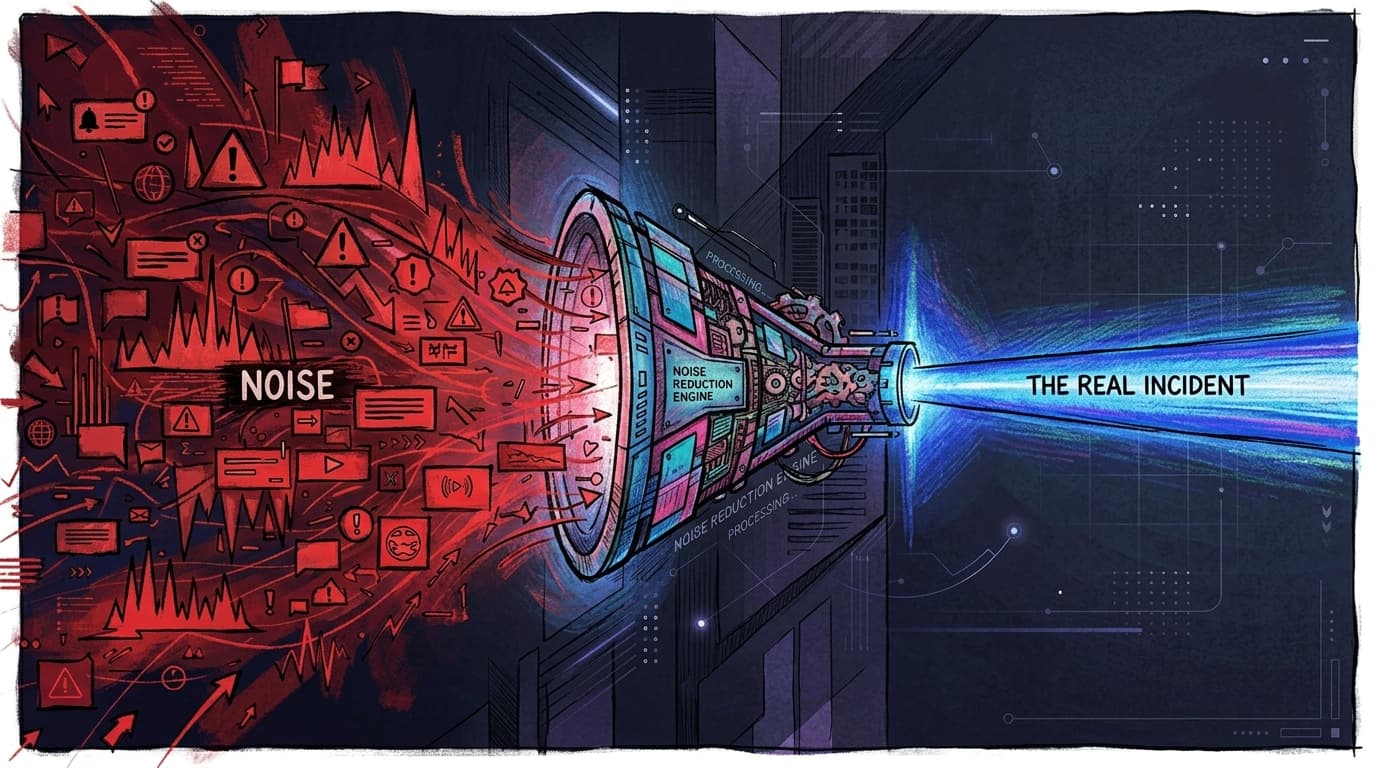
4. The Three Layers of Noise Reduction
Mathematical thresholds form the foundation (Layer 1). However, achieving a full 90% reduction requires implementing all three layers to contextualize the remaining signals.
Alert Funnel Architecture
Translating raw telemetry into actionable signals.
Layer 1: Thresholds
Layer 2: Correlation
Layer 3: Supression
The Compounding Effect
Crucially, while the noise drops by 90%, the miss rate often improves because humans now have the bandwidth to investigate the remaining 50 alerts deeply instead of ignoring them.
5. Practical Implementation Playbook
| Timeframe | Action |
|---|---|
| Weeks 1-2 | Export 90 days of alert history. Categorize as actionable, noise, duplicate. Calculate your current noise ratio. |
| Weeks 3-4 | For the top 10 noisiest alert rules, run the replay analysis. Adjust (V, D) to Pareto-optimal. Deploy behind shadow alerting if possible. |
| Month 2 | Map service dependency graph. Implement symptom grouping for top failure domains (K8s, databases). Add deployment correlation. |
| Month 3+ | Build time-of-day baselines. Implement auto-resolve pattern detection. Consider AI-powered correlation for scale. |
6. How Sherlocks AI Approaches This
Rather than expecting you to spend months building data pipelines to calculate these trade-off surfaces manually, modern platforms take a different path.
- ✓ Investigates everything: Takes your existing alerts as they are and investigates every single one automatically instead of arbitrarily blocking them.
- ✓ The Awareness Graph maintains a live topology, naturally correlating database locks with downstream 500s.
- ✓ Sherlocks maintains historical learnings, trends, and specific contexts (like discussions from Slack channels) in its Knowledge Graph, applying this crucial intelligence during investigations.
- ✓ Provides data-backed recommendations on how to safely adjust your thresholds to reduce future noise.
Result: Teams achieve the 90% noise reduction target in weeks instead of quarters.
7. Key Takeaways
- Alert noise is not an unsolvable problem; it is a quantifiable optimization problem.
- Duration is typically the highest-leverage knob, yet most teams obsess over the threshold value.
- You need all three layers to conquer 90%: Threshold optimization + Correlation + Intelligent Context.
- The future is a closed-loop system where alerts tune themselves based on historical triage outcomes.
Frequently Asked Questions
According to industry data from PagerDuty and other sources, 40-70% of alerts in a typical SRE environment are noise. Some teams report even higher ratios depending on how aggressively they have configured their monitoring. The key issue is that most teams lack the data to quantify their exact noise ratio because they never systematically label alerts as actionable versus non-actionable.
With a manual, data-driven approach using the mathematical framework described in this guide, expect 2-3 months for the full three-layer implementation. Layer 1 (threshold optimization) can show 40-50% reduction in the first 2-4 weeks. AI-powered platforms like Sherlocks.ai can compress this timeline to weeks by automating the investigation and correlation layers.
This is the central concern, and the answer is: done correctly, reducing noise actually improves your detection of real incidents. Alert fatigue is the #1 cause of missed incidents. When engineers are drowning in 500 alerts per week, they inevitably start ignoring them. By reducing to 50 high-signal alerts, each one gets proper attention. The mathematical framework ensures you explicitly quantify your miss rate at every threshold change, so you always know the tradeoff.
Alert suppression is a blunt instrument that silences alerts based on simple rules (time windows, specific sources). Noise reduction is a multi-layered strategy that preserves signal while eliminating false positives. Suppression risks hiding real incidents; proper noise reduction uses statistical thresholds, correlation, and contextual intelligence to ensure every remaining alert is actionable.
It depends on the metric. Slow-moving metrics like disk usage work well with static thresholds. High-frequency, variable metrics like CPU utilization and latency benefit enormously from dynamic baselines that account for time-of-day patterns and seasonal variation. The key insight from this guide is that the duration window (D) is often more impactful than the threshold value itself, regardless of whether you use static or dynamic approaches.
Start by quantifying the cost. Calculate: (number of noisy alerts per week) x (average time to triage each) x (engineer hourly cost). For most teams, this translates to tens of thousands of dollars per month in wasted engineering time, plus the hidden costs of burnout and attrition. Run a 2-week labeling exercise on your top 10 noisiest alert rules to build a concrete business case.
Tired of alert fatigue?
See how Sherlocks AI automates alert tuning and causal correlation natively, bypassing multi-quarter data engineering efforts.
Try Sherlocks Free →